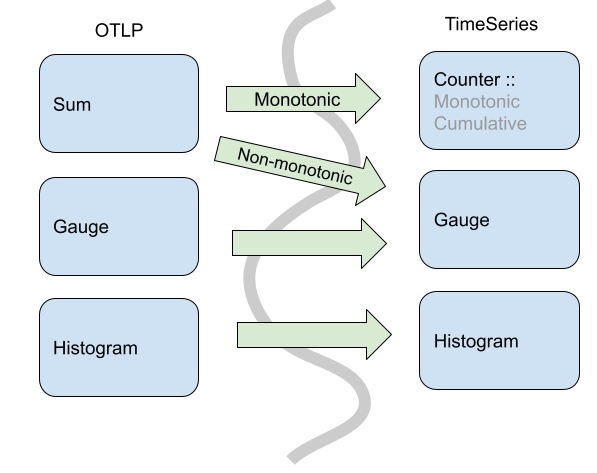
Three typical solutions of counter in the SRN state space: a) monotonic... | Download Scientific Diagram
![PDF] Virtual monotonic counters and count-limited objects using a TPM without a trusted OS | Semantic Scholar PDF] Virtual monotonic counters and count-limited objects using a TPM without a trusted OS | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/1fc71807dd748cde9798f1b305bc58c1252b0d38/5-Figure1-1.png)
PDF] Virtual monotonic counters and count-limited objects using a TPM without a trusted OS | Semantic Scholar
PPT - Correction to Pseudo-Code in “Virtual Monotonic Counters and Count-Limited Objects” Paper PowerPoint Presentation - ID:441374

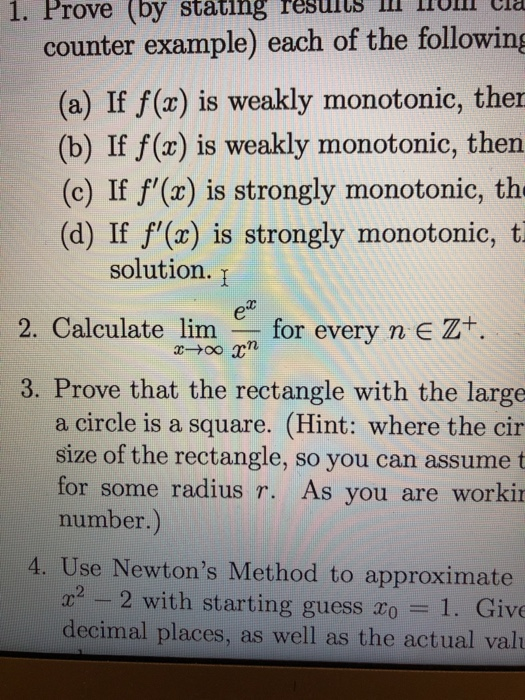
SOLVED: Decide il each of the statements below is true or false. If it is true, give a complete proof; if it is false, give an explicit counter- example: There exists monotonic

PPT – Virtual Monotonic Counters and Count-Limited Objects Using a TPM without a Trusted OS PowerPoint presentation | free to download - id: 201c1-NWE3M

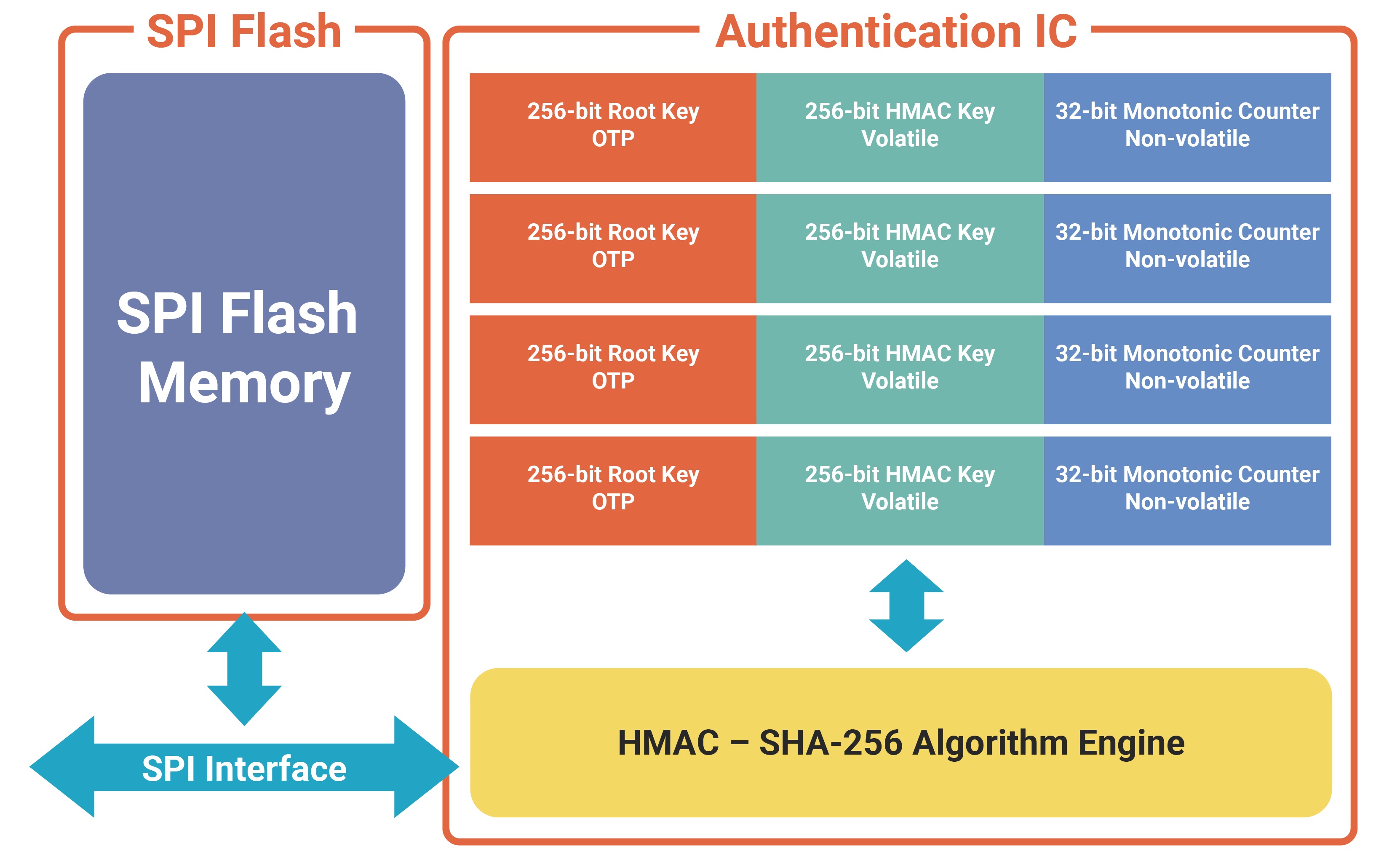
Virtual Monotonic Counters and Count-Limited Objects Using a TPM without a Trusted OS Luis F. G. Sarmenta Joint work with: Marten van Dijk. - ppt download